Optimizing Wordfence Security Settings: Brute Force Protection
As a part of the Wordfence Client Partner initiative, we’ve recently had some in depth conversations with organizations using Wordfence at scale. These conversations have been enlightening, and we wanted to share some of the stories we’ve heard about how different organizations use Wordfence.
This post is Copyright 2018 Defiant, Inc. and was published on the wordfence.com official blog. Republication of this post without permission is prohibited. You can find this post at: https://www.wordfence.com/blog/2018/07/optimizing-wordfence-security-settings-brute-force-protection/
Wordfence is the most robust security solution available for WordPress site owners, and the number of security features available is unparalleled. This ensures that Wordfence can be customized to be an optimal security solution for your specific environment and security needs.
Getting Started with Wordfence
When you install Wordfence for the first time, the plugin defaults to recommended settings that are a perfect starting place for customization. You won’t need to do much else. However, Wordfence is highly configurable, allowing you to tailor how it works to meet your needs.
How our Customers Use Brute Force Protection:
Wordfence includes a number of powerful brute force protection features that can be used to prevent malicious bots from gaining access to your site, including the integration with Troy Hunt’s version 2 of the Pwned Passwords API that prevents access using passwords previously seen in a breach. In this post we will focus on Brute Force Protection and how our customers can customize this feature, based on their security needs.
Factors to consider when modifying your site’s Brute Force Protection settings include:
- How adept are your users? Do you have users that forget their passwords often? Are they logging in sporadically and have a high probability of losing their passwords? You’ll want to take them into consideration and allow room for user error.
- Is this a high traffic, high profile site that often experiences hacking attempts?
- Is your site under repeated attack from brute force attempts?
The following customer scenarios serve as great real-world examples of how Wordfence can be customized to meet specific needs.
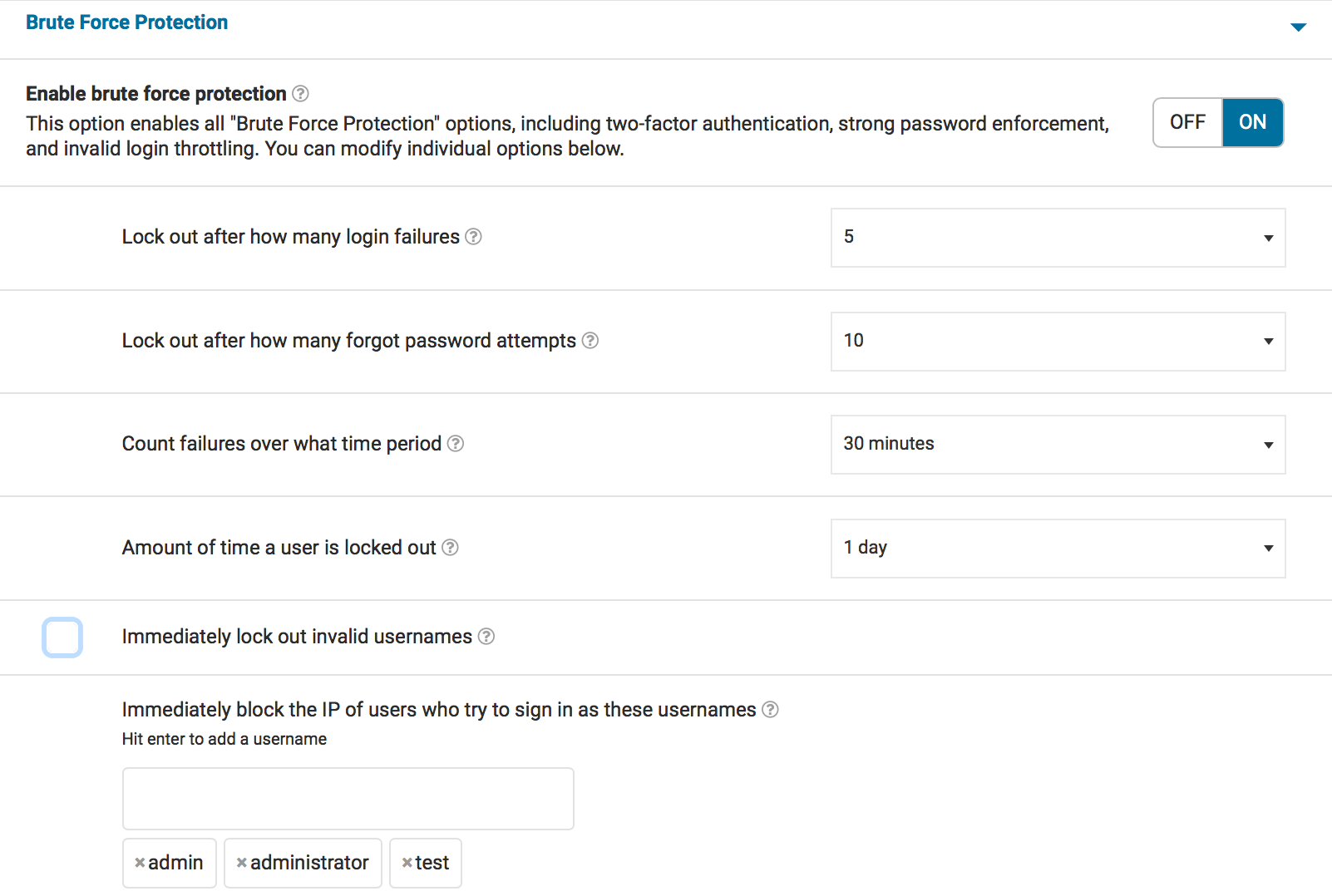
Kyle’s Agency Customer Site
One of our agency partners, Kyle, manages a number of WordPress installations for his customers. His customers rarely perform any administrative tasks, but they have editor access in order to add and modify new content. The agency has administrator access, and they have set up Wordfence Premium to protect the site. In addition to the premium features of country blocking and two-factor authentication for administrators only, he has tightened Brute Force Protection. Some of his customers often forget their passwords, and he wants to ensure they can still access the site to post content without causing too much administrative work for his team.
Kyle sets up his sites so that failed logins lockout after 5 attempts, forgot password attempts are set to 10 and a user is locked out for 24 hours. He does not set the site to immediately lock out invalid usernames, but he immediately blocks anyone who uses ‘admin’, ‘administrator’, or any other failed logins he sees. He routinely audits his site’s failed logins and adjusts this setting accordingly.
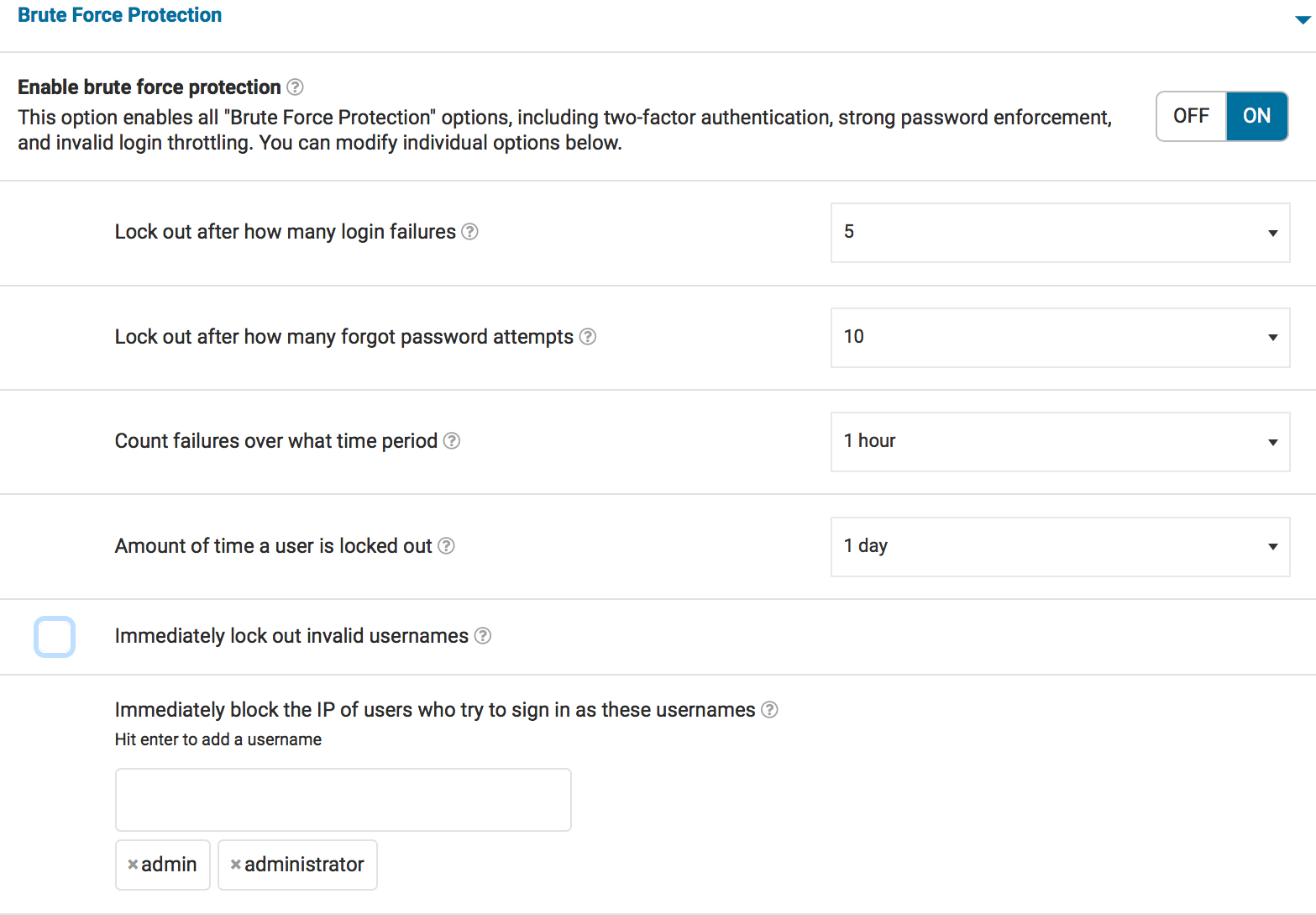
Maria’s Membership Site
Maria uses Wordfence on a WordPress membership site. She has a team of publishers and administrators and a large number of members who need to login in order to access content. Some of them use good password hygiene, but others do not. Maria’s site is also protected by Wordfence Premium, and she has made some adjustments to her brute force protection settings.
Maria has set her failed logins lockout to 5 attempts, forgot password attempts are set to 10, and a user is locked out for 24 hours. She does not set the site to immediately lock out invalid usernames because she has a large user base. She immediately blocks anyone who uses ‘admin’ or ‘administrator’, but does not go further than that. She uses Wordfence Premium’s two-factor authentication and some minor country blocking to augment her site’s security.
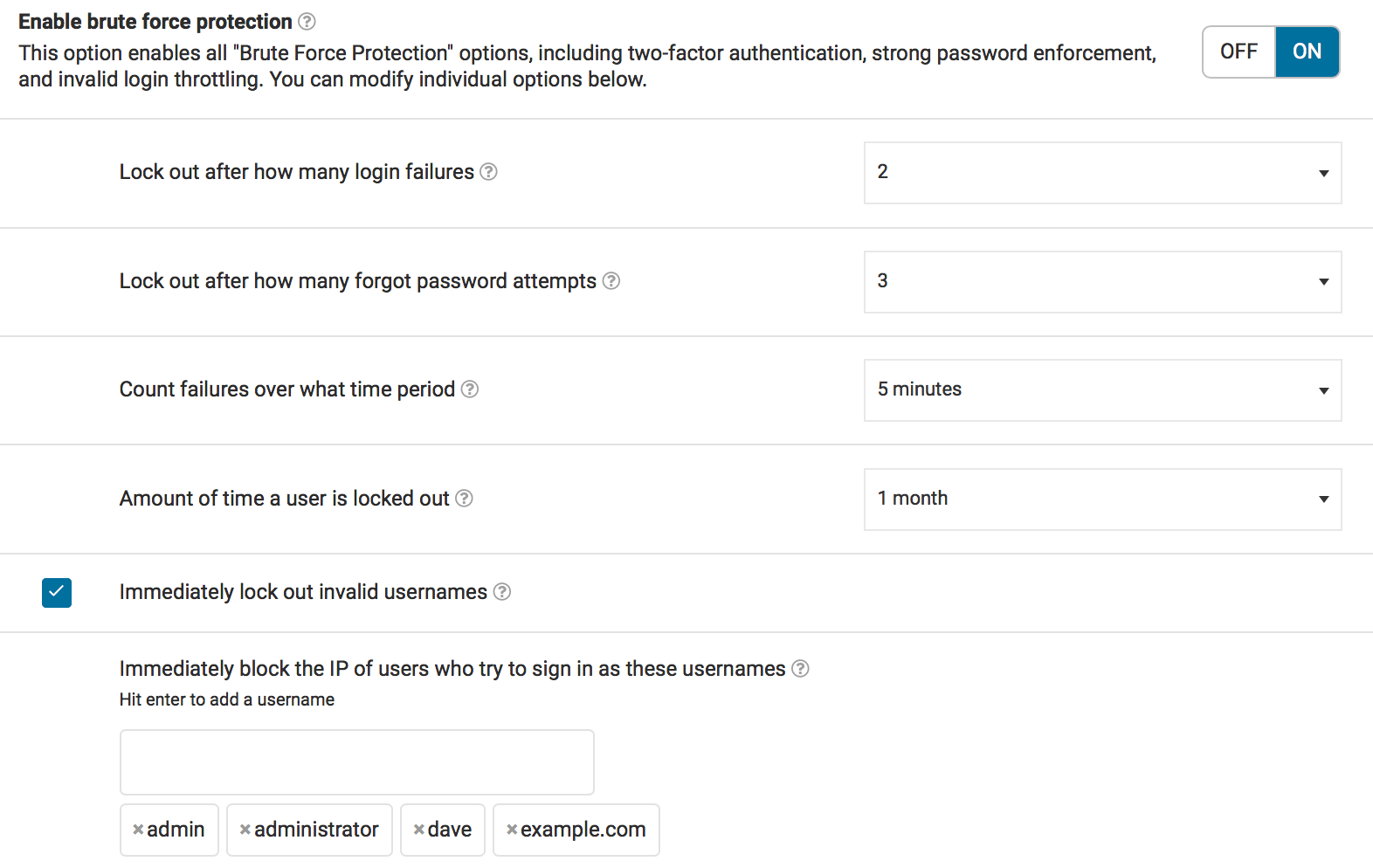
Dave’s Personal Site
Dave has a personal blog. He has one login for himself and no other users. He knows his password, and also has access to FTP in order to easily deactivate Wordfence if he ever locks himself out. He has tightened his Brute Force Protection settings because he’s quite confident in his ability to store his password safely.
Dave sets up his sites so that failed logins lockout after 2 attempts, forgot password attempts are set to 3, and IP addresses that reach these limits are locked out for one month. He immediately locks out any invalid users and also immediately blocks anyone who uses ‘admin’, ‘administrator’, or any other failed logins he sees.
He also uses two-factor authentication to ensure that logging in is difficult for anyone other than himself should his credentials ever be discovered.
Sam’s Small e-commerce Site
Sam has a small e-commerce site that is growing rapidly. He has a number of contractors on the site updating product information. He has users that need to login for various business functions and needs to ensure that everyone can log in, but doesn’t want to risk his site’s security given how sensitive e-commerce data is. He’s invested in Wordfence Premium and requires his administrators to use two-factor authentication for logging in.
Sam sets up his sites so that failed logins lockout after 5 attempts, forgotten password attempts are set to 5, and a user is locked out for 4 hours. He does not set the site to immediately lock out invalid usernames. He has set his Wordfence installation to block any passwords from data breaches to anyone who can publish as well as administrators because of the turnover in the contractors he is using to update product information.

How are you using Brute Force Protection?
We hope this deeper look at our Brute Force Protection settings has been helpful. If you’ve been using Wordfence for a while, how are you using Brute Force Protection? Are there rules you’ve set that work well for your unique site requirements?
Are you seeing any new brute force attack patterns that concern you? Let us know in the comments.
We’ll be covering more ways that our customers use Wordfence in upcoming posts.
The post Optimizing Wordfence Security Settings: Brute Force Protection appeared first on Wordfence.